macOS security and com.apple.quarantine extended attribute
Apple offers one of the most advanced operating systems out there: macOS. With security and privacy in its core, it comes with a number of system protection services such as Gatekeeper runtime protection, the built-in System Integrity Protection (SIP), and others. While Apple Software, Apple installers and apps from the App Store are already cleared […]
PHP-FPM settings for best performance

A recurring question we get from customers is how to fine tune PHP-FPM settings. The official PHP documentation kind of lacks recommendations in this regard. So we’ve made this article explaining how you can calculate the optimal PHP-FPM settings for your server. PHP-FPM is an acronym for PHP FastCGI Process Manager, one of the most […]
Install docker & docker-compose on Oracle Linux
By default on the new Enterprise Linux distributions, docker engine has been replaced by podman, a docker compliant engine. In order to install docker and docker-compose, you can follow this simple tutorial. Install Docker Engine To install docker engine we’ll add first the docker repository: And now we can proceed to install docker: And we […]
How to mount a VHD disk image file

Sometimes you may need to mount a VHD disk image file in order to inspect its contents or even recover specific files. On Linux you can use the QEMU Disk Network Block Device Server utility – qemu-nbd – to access disk images in different formats as if they were block devices. First, you may want […]
How To Create a SSH Key

In this tutorial we will explain how you create a SSH Key pair and how to use this key to authenticate on remote devices. SSH, that stands for Secure Shell, is a network protocol used to establish an encrypted connection between two devices. The SSH protocol supports either the use of a username and password […]
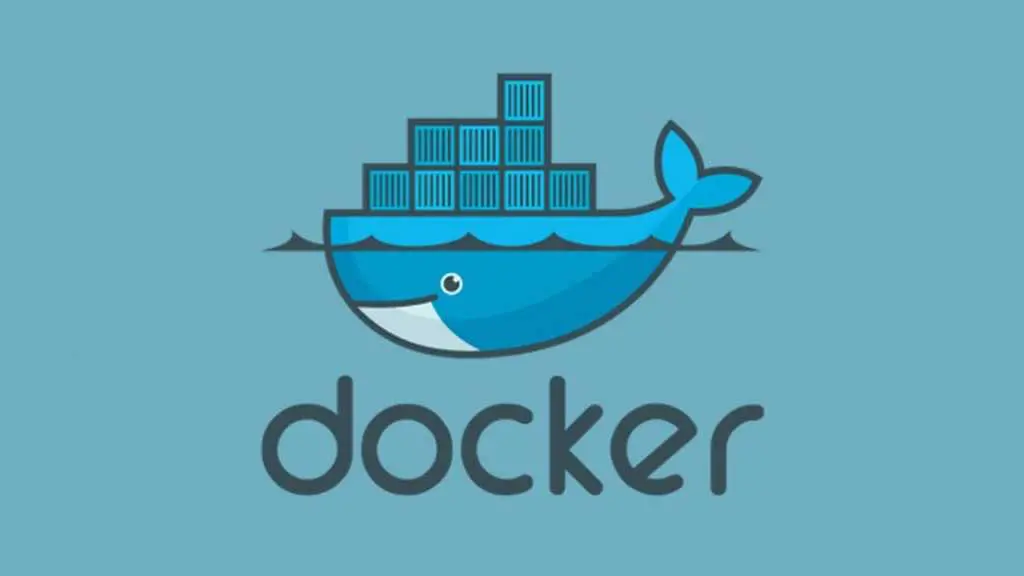
Microsoft blocks Windows Defender ability following major security concerns
Microsoft has blocked the ability to download files using Windows Defender after it was shown how easily it could be used by attackers to install malware onto a computer. Earlier this year, for reasons yet unclear, Microsoft discreetly added the ability to download files using Windows Defender. When this was publicly recognized, there was grave concern from […]
Windows 10 themes can be abused to steal passwords
Security researcher Jimmy Bayne (@bohops) has revealed that specially crafted Windows themes can be used to perform Pass-the-Hash attacks and steal passwords. Pass-the-Hash attacks are used to steal Windows login names and password hashes by tricking the user into accessing a remote SMB share that requires authentication. A theme’s settings are saved under the %AppData%\Microsoft\Windows\Themes folder as a […]
Web security is improving, but so much more to be done

A much-anticipated report from Rapid7, a cybersecurity company based in Boston USA, revealed “frankly shocking” news concerning the current global state of security on the Internet in the wake of the Covid-19 pandemic. According to the massive cross-industry study, completed in the summer of 2020, the findings revealed that despite enormous security problems from the […]
Google’s Android Lockbox spying competitor apps

Revelations have emerged from reported sources that Google is spying on how people interact with rival Android apps. The report mentions how Google is monitoring users interactions with non-Google apps via an internal program and utilizing the data to improve its own products. According to a startling report in The Information, a program called Android Lockbox gives […]
Developers ignoring software testing automation

A tough, agile system strategy is critical to all organizations but, according to a new survey, less than 80% of developers are automating fewer than half their tests. Proper software testing ensures the launch of a new software system can implement smoothly and is an essential tool for project managers. The operation of any software […]